Blog
Security research, vulnerability analysis, and product updates.

Move Smart Contract Security: What Sui and Aptos Developers Need to Know
Move eliminates reentrancy and integer overflow by design. The vulnerabilities that remain are specific to Move's resource model, and most developers coming from Solidity or Rust are not looking for them.
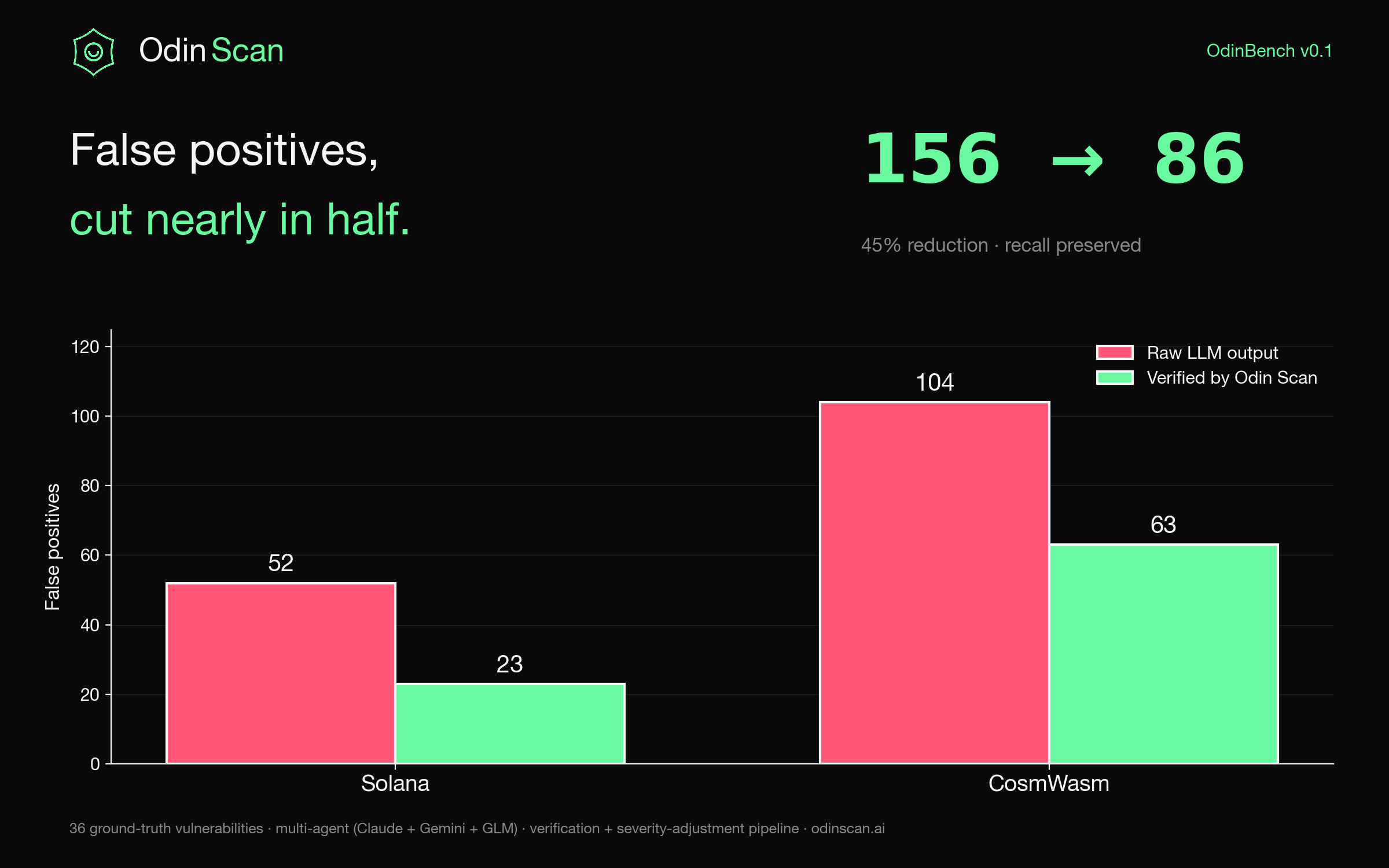
OdinBench v0.1: Measuring False Positives in LLM Security Scanners
Most AI security scanners ship without measuring themselves. We didn't. On 38 contracts across Solana and CosmWasm, our verification pipeline cuts false positives 45% while preserving recall, and on EVM every Critical-severity finding is a real bug.

CI/CD for Smart Contracts: Automated Security in Your Development Pipeline
Audits happen once. Code changes every day. Here is how to build a CI/CD pipeline that catches smart contract vulnerabilities on every PR, before they reach mainnet.
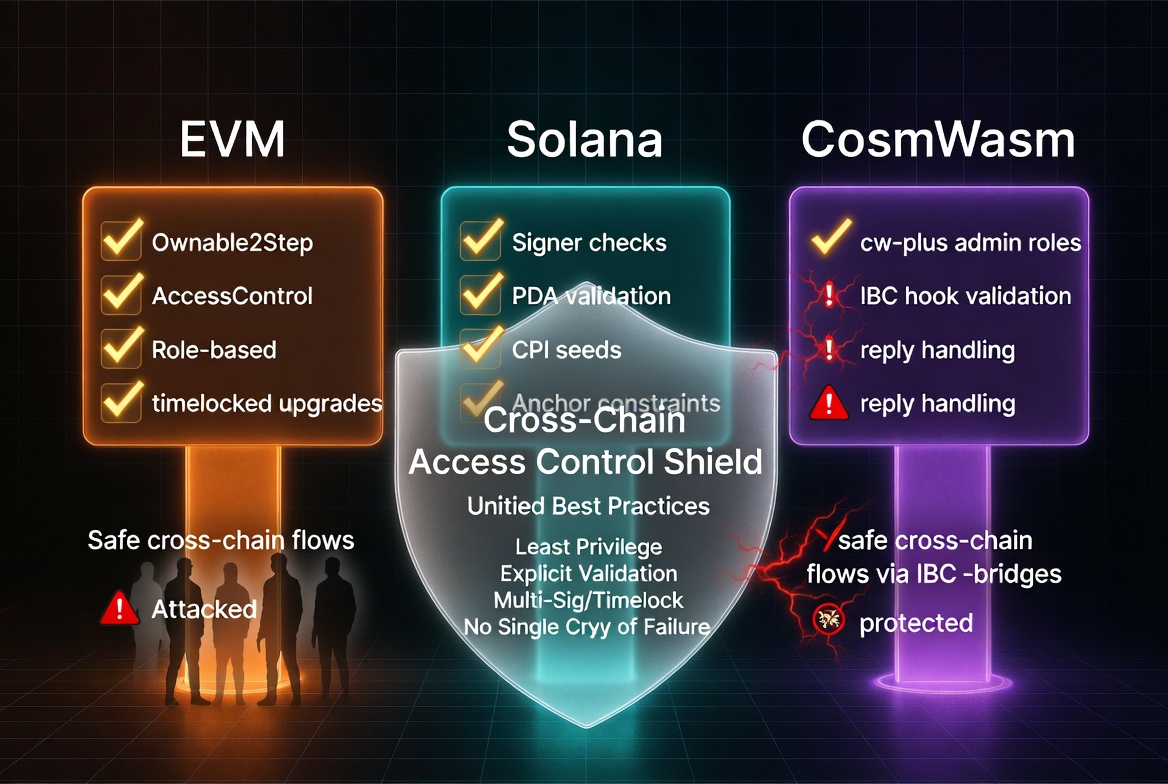
DeFi Access Control Patterns: A Cross-Chain Checklist
Missing access control is the number one critical finding in smart contract audits across every chain. Here are the patterns for EVM, Solana, and CosmWasm, with the specific mistakes auditors keep finding.
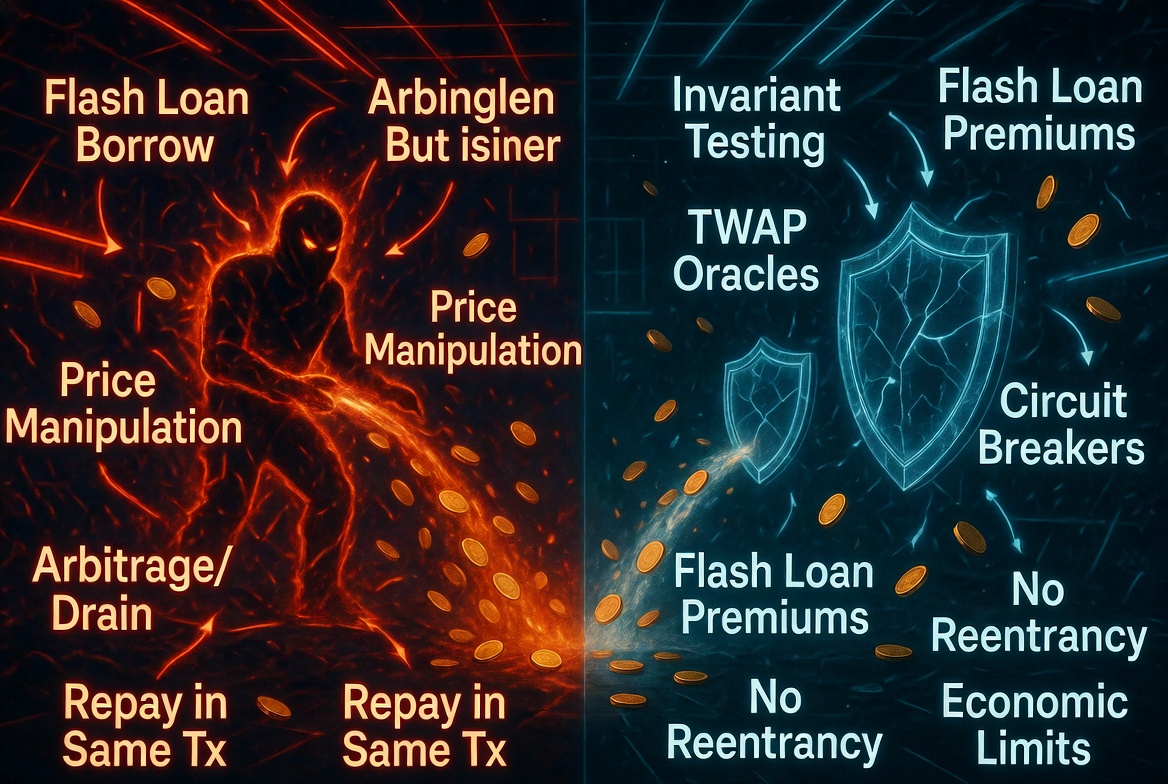
Flash Loan Attack Playbook: How Attackers Think and How to Defend
Flash loans do not create vulnerabilities. They make existing ones profitable. Here is how attackers construct flash loan exploits step by step, and the specific design patterns that neutralize them.
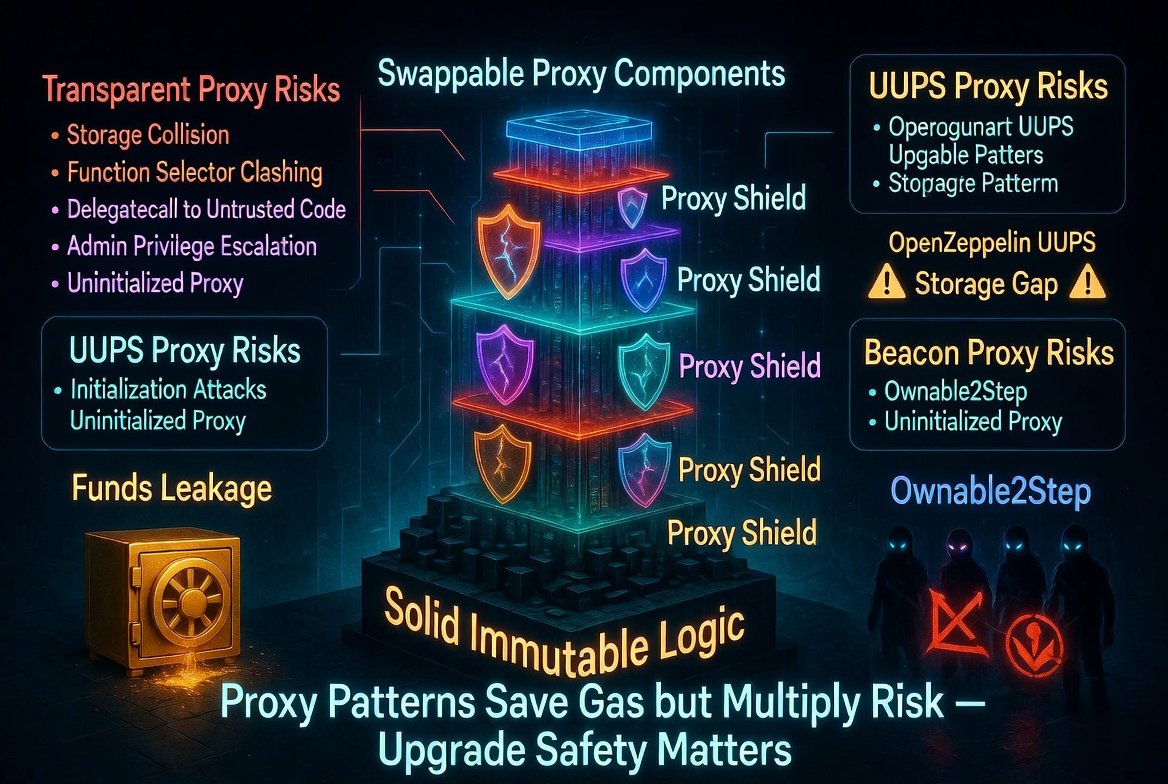
Smart Contract Upgrade Safety: Proxy Patterns and Their Pitfalls
Upgradeable contracts let you fix bugs after deployment. They also let you introduce new ones. Here are the proxy patterns, their trade-offs, and the specific mistakes that cause storage corruption, bricked contracts, and stolen funds.
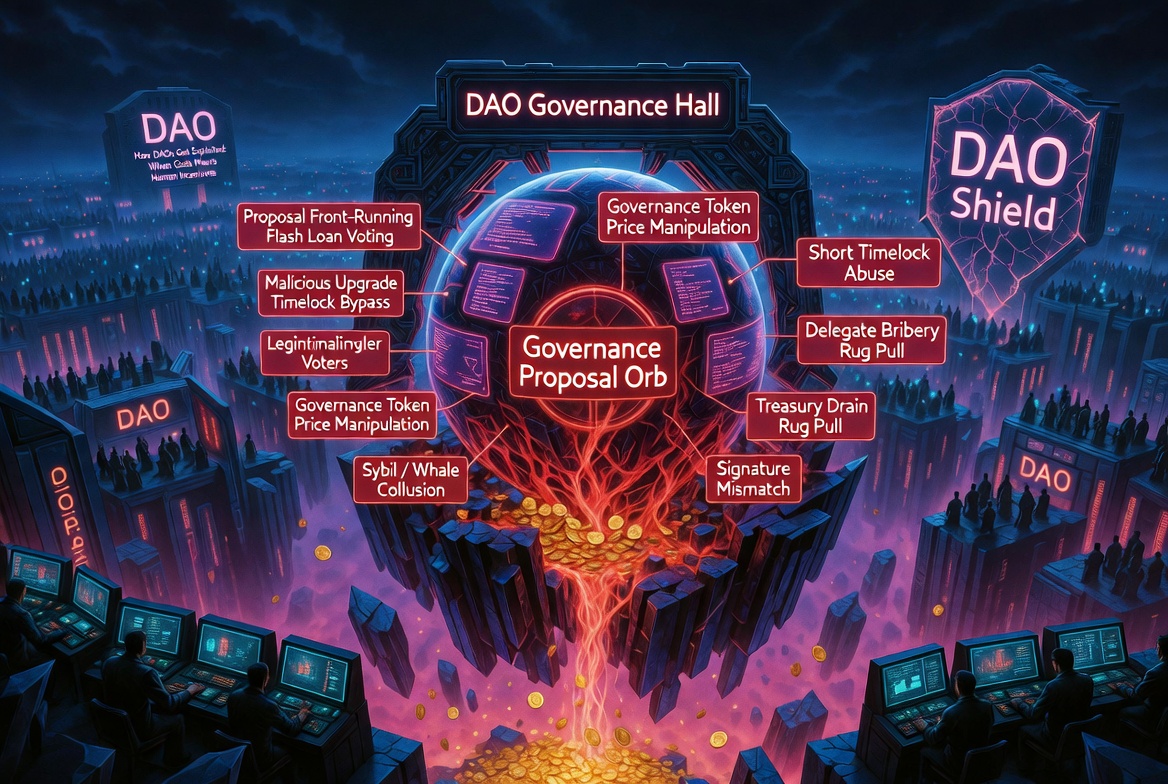
Governance Attack Vectors: How DAOs Get Exploited
Governance proposals execute with the highest privilege level in a protocol. They are also the least scrutinized code path. Here is how attackers exploit that gap.
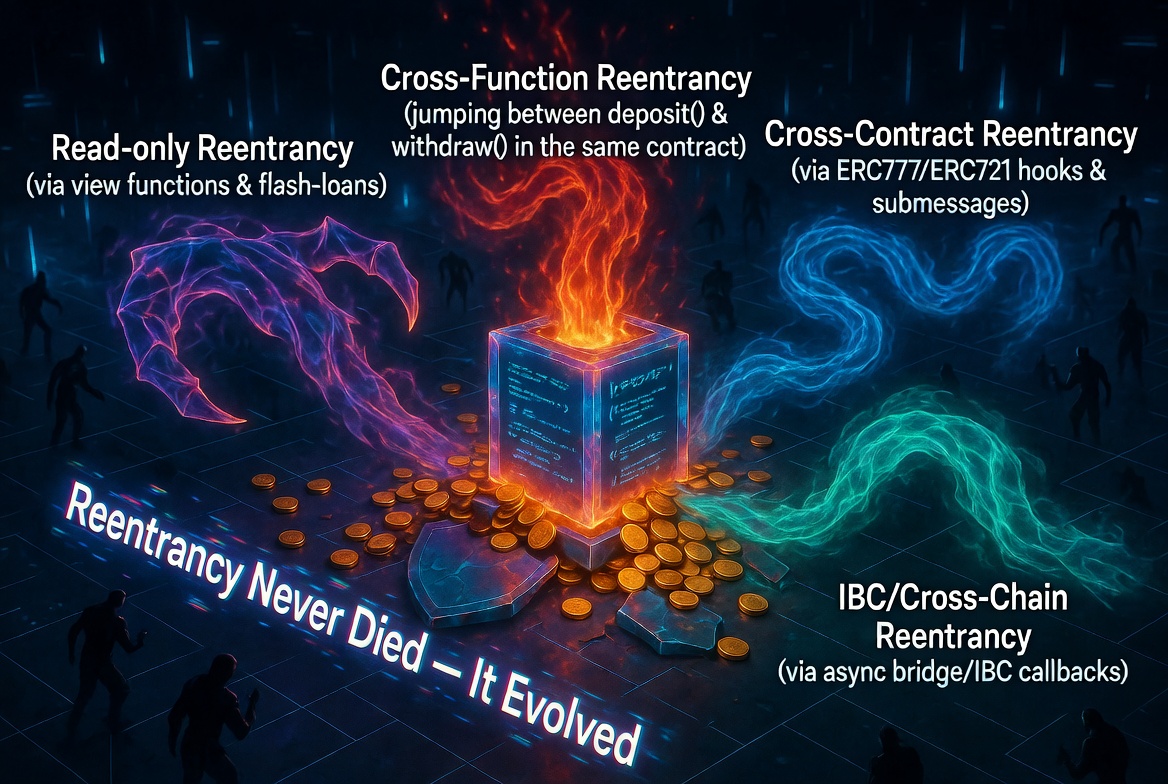
Reentrancy in 2026: The Bug That Refuses to Die
Ten years after The DAO hack, reentrancy is still draining protocols. The classic variant is well-understood. The modern variants are not. Here is what reentrancy looks like in 2026.
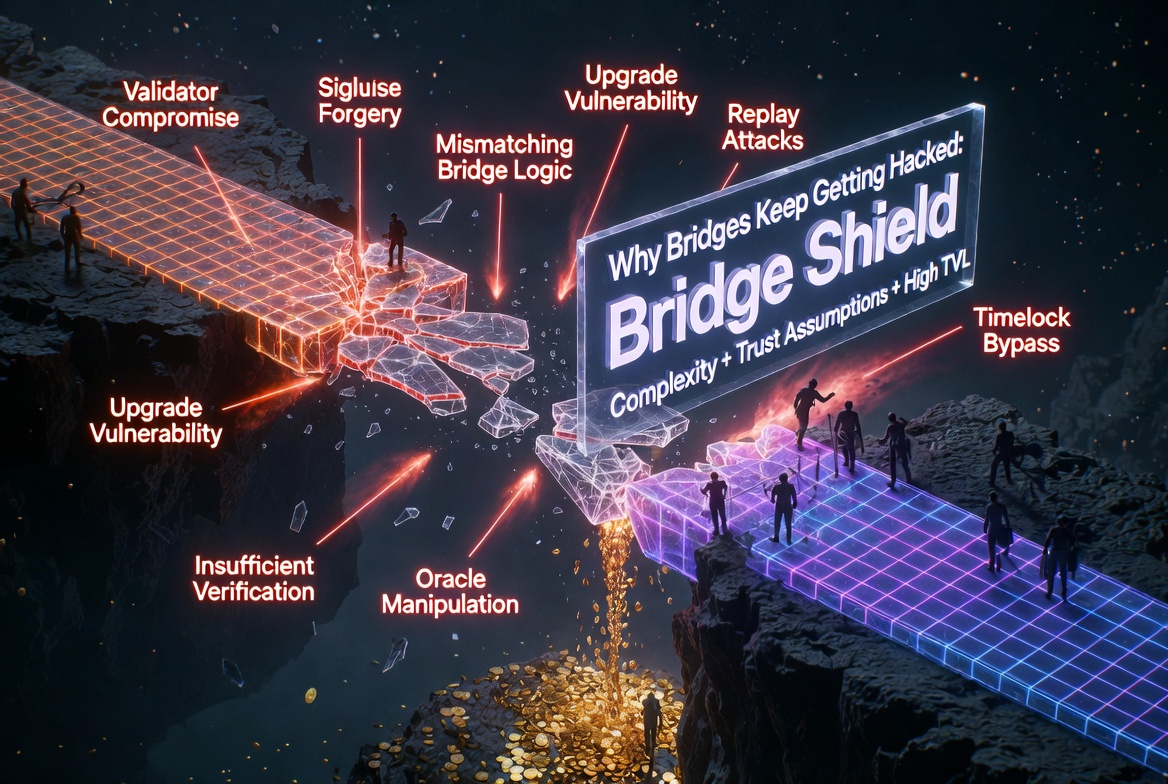
Cross-Chain Bridge Security: Why Bridges Keep Getting Hacked
Bridges are the highest-value targets in crypto. Over $2.5 billion stolen since 2021. The attack surface is unique, the stakes are enormous, and the same patterns repeat.