Blog
Security research, vulnerability analysis, and product updates.

Drift Lost $285M to a 6-Month Con. The Smart Contract Was Fine.
On April 1, Drift Protocol lost $285M in 12 minutes. There was no smart contract bug. The attackers spent six months getting the Security Council to pre-sign their own rug.
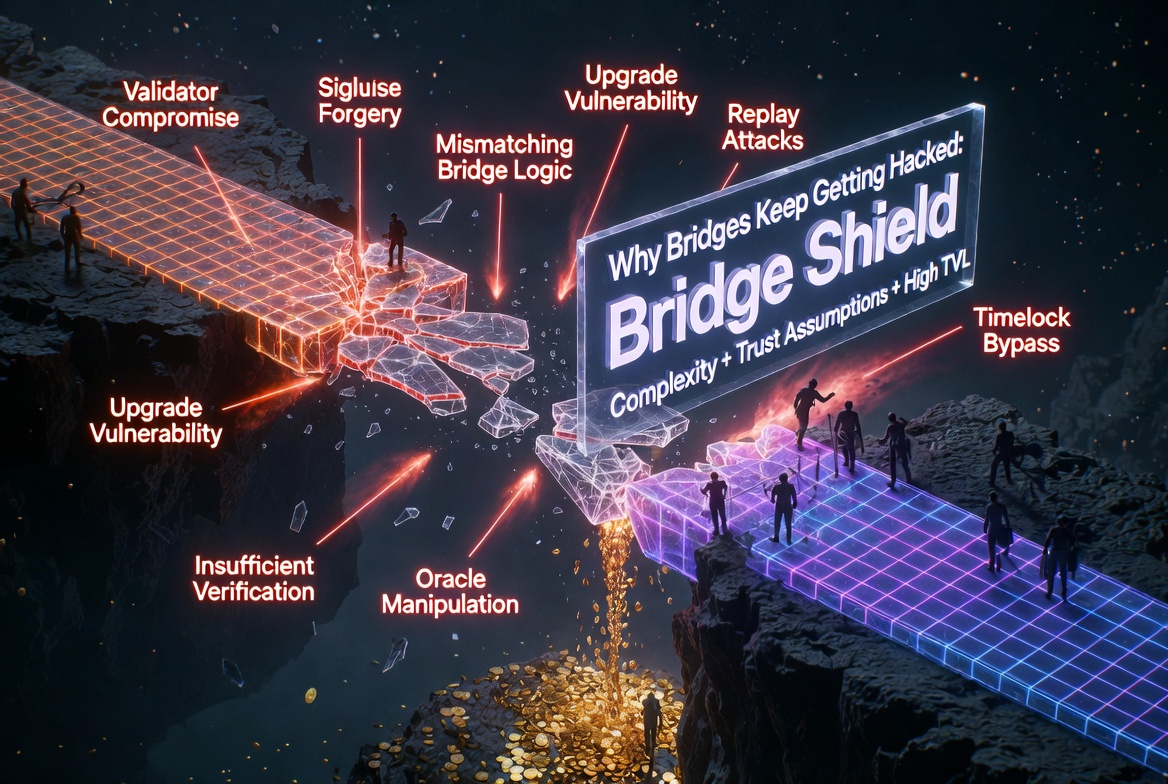
Cross-Chain Bridge Security: Why Bridges Keep Getting Hacked
Bridges are the highest-value targets in crypto. Over $2.5 billion stolen since 2021. The attack surface is unique, the stakes are enormous, and the same patterns repeat.

The Top 10 Smart Contract Vulnerabilities in 2025: Lessons from Real Exploits
2025 saw over $2 billion stolen from smart contracts. These are the 10 vulnerability patterns responsible for the largest losses, ranked by total damage.

Aave's $27M Glitch: When the Oracle Was Right and the Cap Was Wrong
On March 10, a snapshot parameter drifted against its timestamp on Aave's CAPO oracle. 34 users got liquidated for $27M against a capped wstETH rate that no longer reflected reality.
Solv Protocol Lost $2.7M to Reentrancy. The Contract Was Unaudited.
On March 5, an attacker turned 135 BRO tokens into 567 million through an ERC-3525 callback reentrancy on Solv Protocol. The vault had no reentrancy guard. It had no audit either.

The Bybit $1.5B Hack: How a Safe Multisig Was Drained
On February 21, 2025, the Lazarus Group stole $1.5 billion from Bybit in the largest crypto hack in history. The multisig was fine. The UI was not.
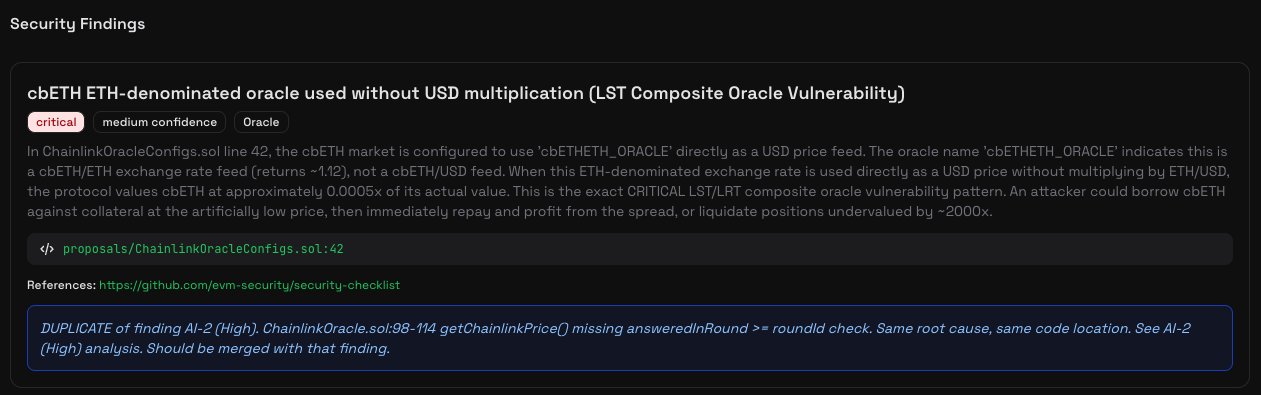
AI Wrote It. AI Caught It. Moonwell Lost $1.78M Anyway.
On February 15, Moonwell lost $1.78M to a cbETH oracle misconfiguration introduced in an AI-assisted PR. Odin Scan had flagged the exact vulnerability as Critical before it ever went live.