Blog
Security research, vulnerability analysis, and product updates.
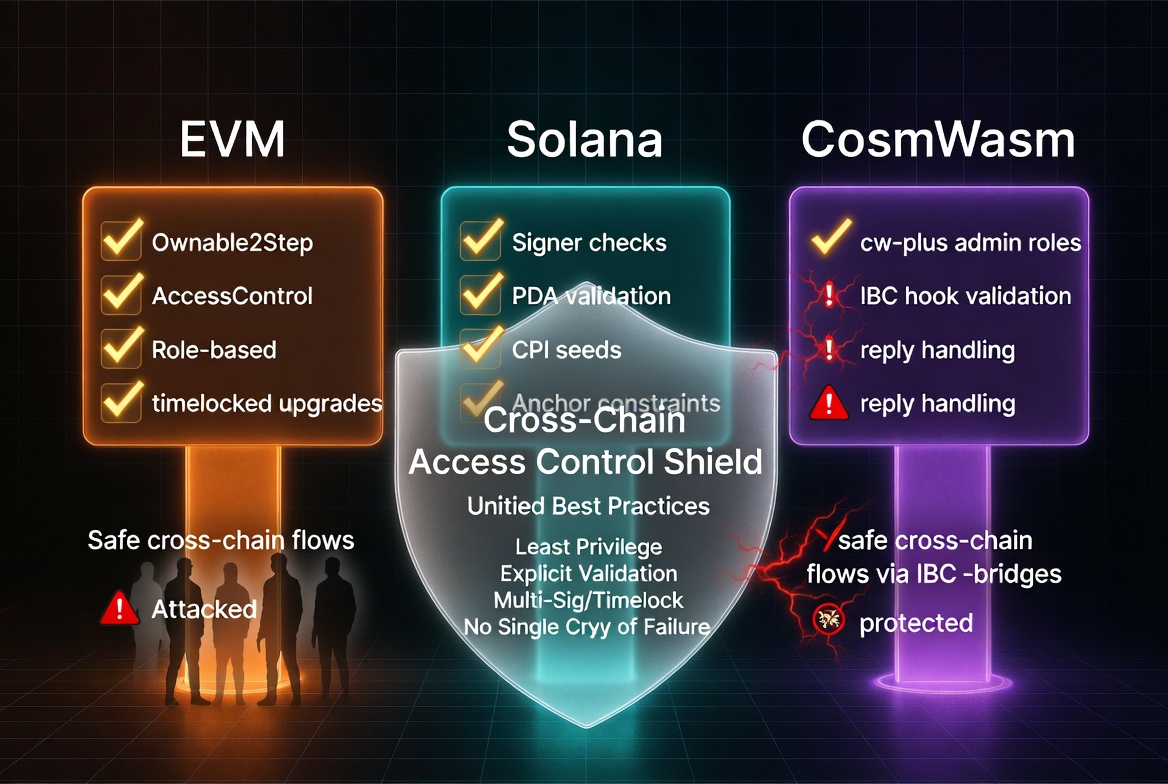
DeFi Access Control Patterns: A Cross-Chain Checklist
Missing access control is the number one critical finding in smart contract audits across every chain. Here are the patterns for EVM, Solana, and CosmWasm, with the specific mistakes auditors keep finding.
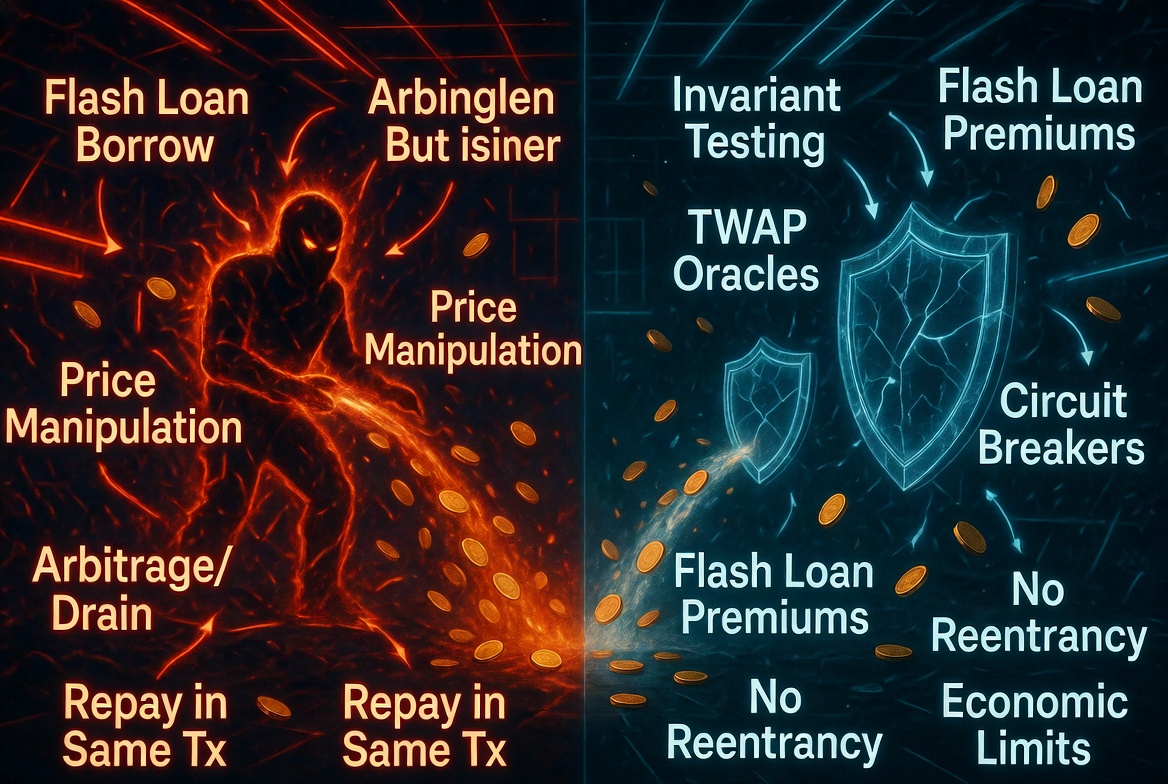
Flash Loan Attack Playbook: How Attackers Think and How to Defend
Flash loans do not create vulnerabilities. They make existing ones profitable. Here is how attackers construct flash loan exploits step by step, and the specific design patterns that neutralize them.
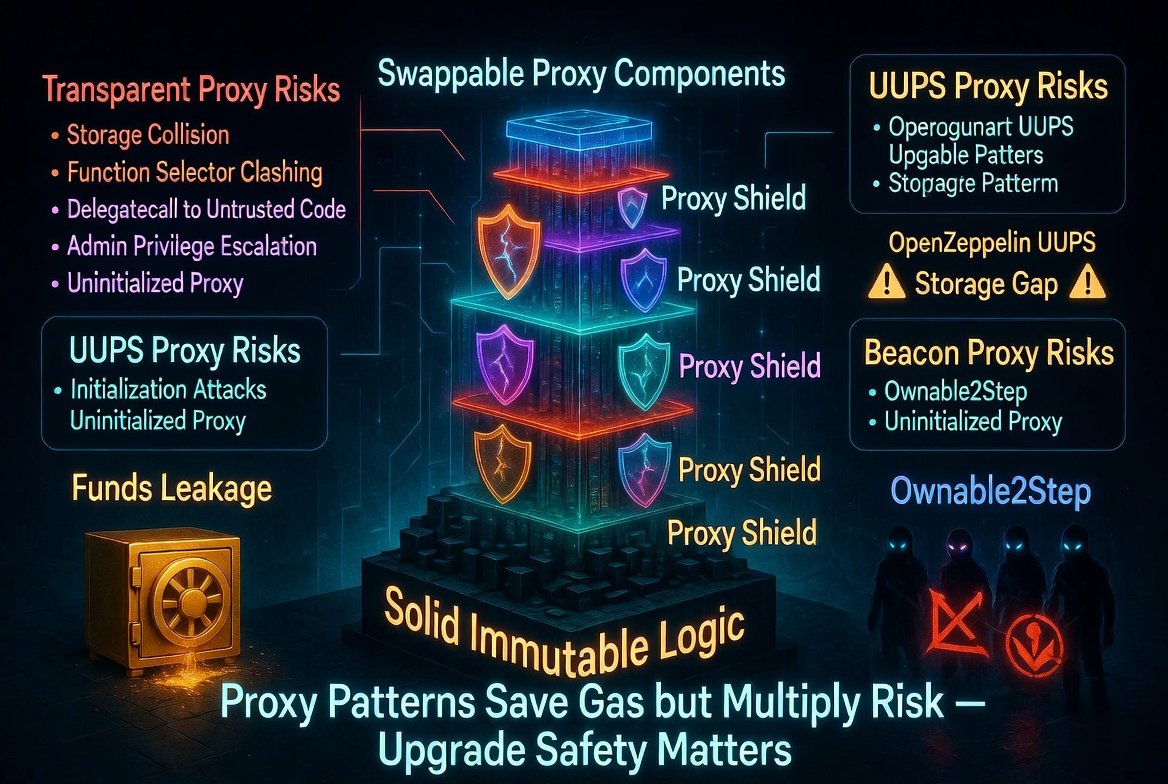
Smart Contract Upgrade Safety: Proxy Patterns and Their Pitfalls
Upgradeable contracts let you fix bugs after deployment. They also let you introduce new ones. Here are the proxy patterns, their trade-offs, and the specific mistakes that cause storage corruption, bricked contracts, and stolen funds.
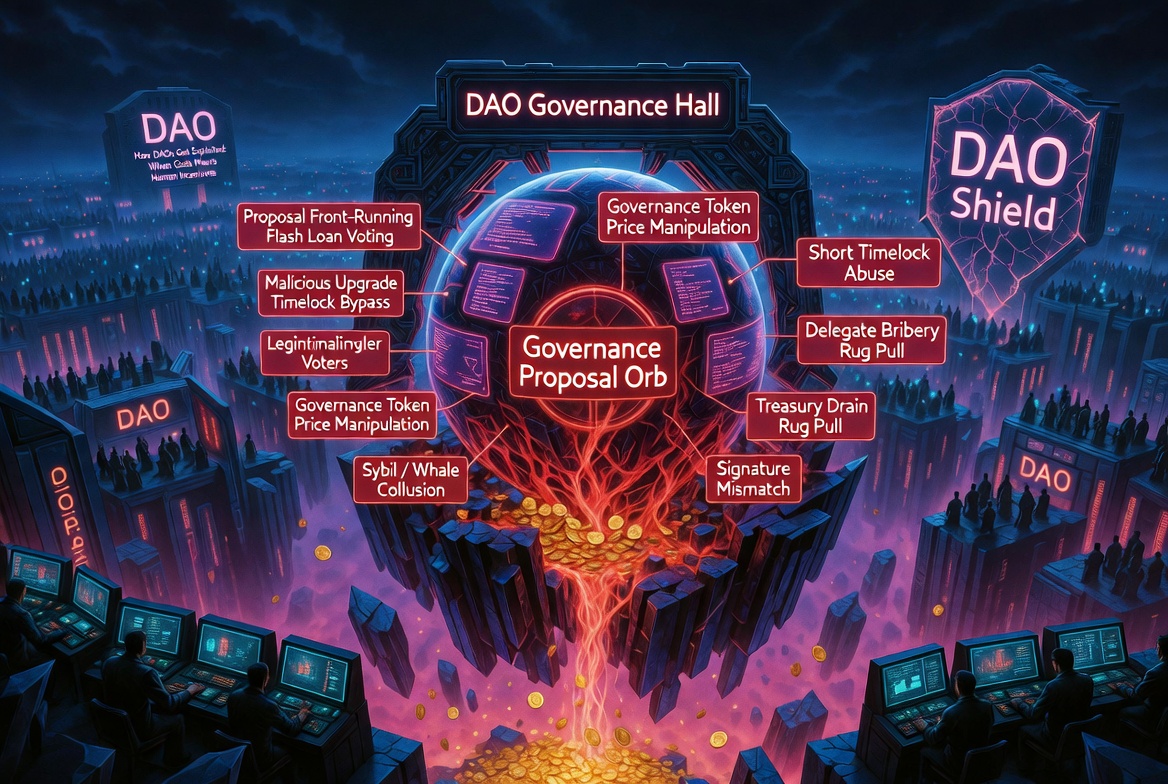
Governance Attack Vectors: How DAOs Get Exploited
Governance proposals execute with the highest privilege level in a protocol. They are also the least scrutinized code path. Here is how attackers exploit that gap.
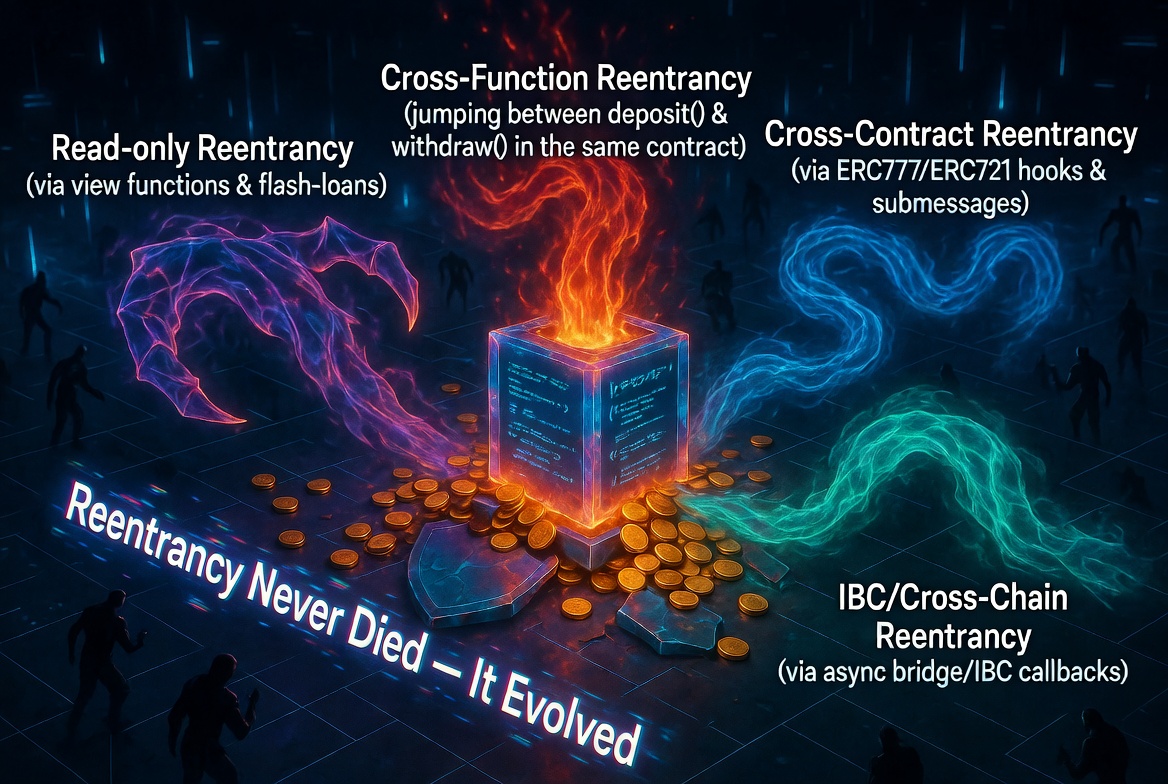
Reentrancy in 2026: The Bug That Refuses to Die
Ten years after The DAO hack, reentrancy is still draining protocols. The classic variant is well-understood. The modern variants are not. Here is what reentrancy looks like in 2026.
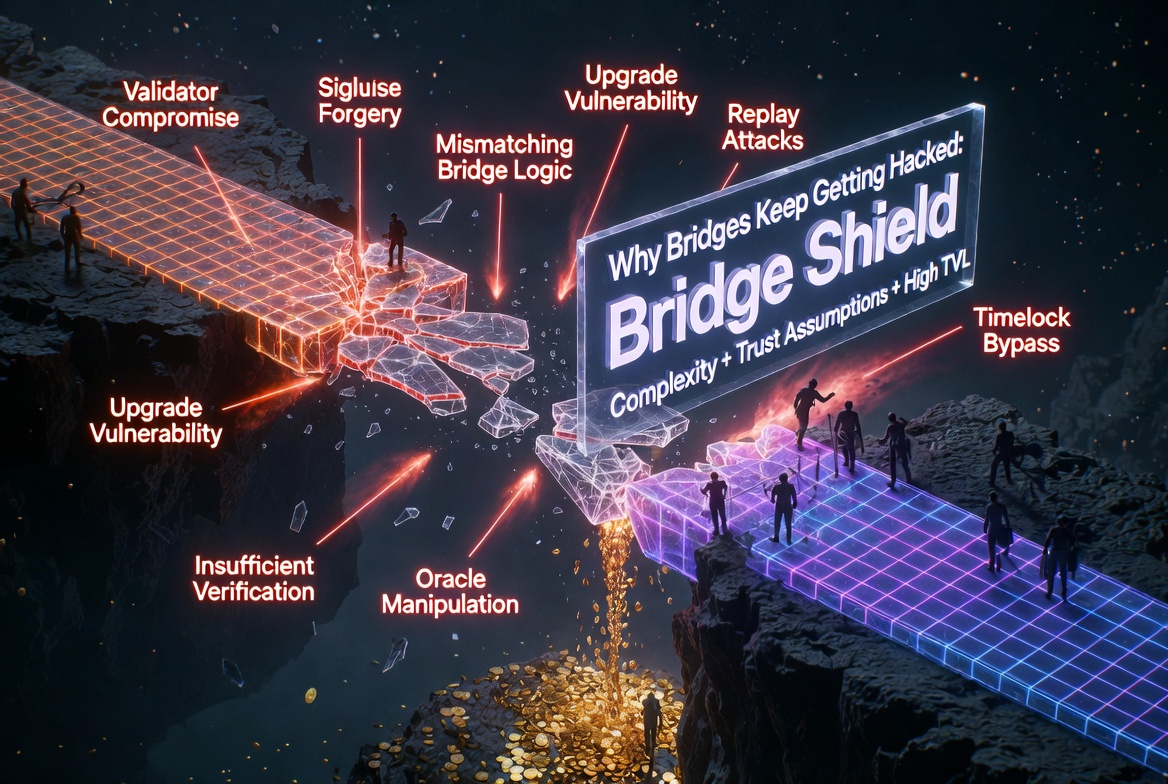
Cross-Chain Bridge Security: Why Bridges Keep Getting Hacked
Bridges are the highest-value targets in crypto. Over $2.5 billion stolen since 2021. The attack surface is unique, the stakes are enormous, and the same patterns repeat.

The Top 10 Smart Contract Vulnerabilities in 2025: Lessons from Real Exploits
2025 saw over $2 billion stolen from smart contracts. These are the 10 vulnerability patterns responsible for the largest losses, ranked by total damage.

Aave's $27M Glitch: When the Oracle Was Right and the Cap Was Wrong
On March 10, a snapshot parameter drifted against its timestamp on Aave's CAPO oracle. 34 users got liquidated for $27M against a capped wstETH rate that no longer reflected reality.

EVM Smart Contract Security: The Developer's Practical Guide
Billions lost. Mostly to the same handful of bugs. Here is the complete practical guide to EVM smart contract security: what the vulnerabilities are, why they happen, and how to prevent them.