Blog
Security research, vulnerability analysis, and product updates.

Move Smart Contract Security: What Sui and Aptos Developers Need to Know
Move eliminates reentrancy and integer overflow by design. The vulnerabilities that remain are specific to Move's resource model, and most developers coming from Solidity or Rust are not looking for them.
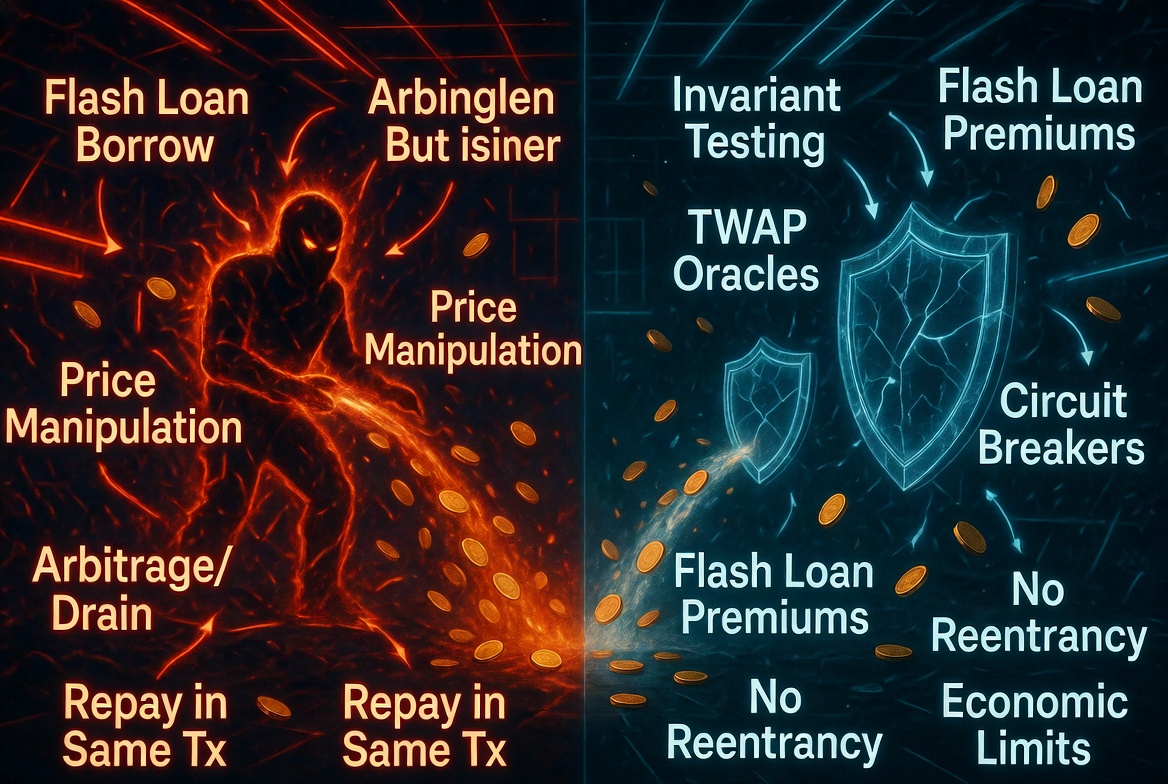
Flash Loan Attack Playbook: How Attackers Think and How to Defend
Flash loans do not create vulnerabilities. They make existing ones profitable. Here is how attackers construct flash loan exploits step by step, and the specific design patterns that neutralize them.
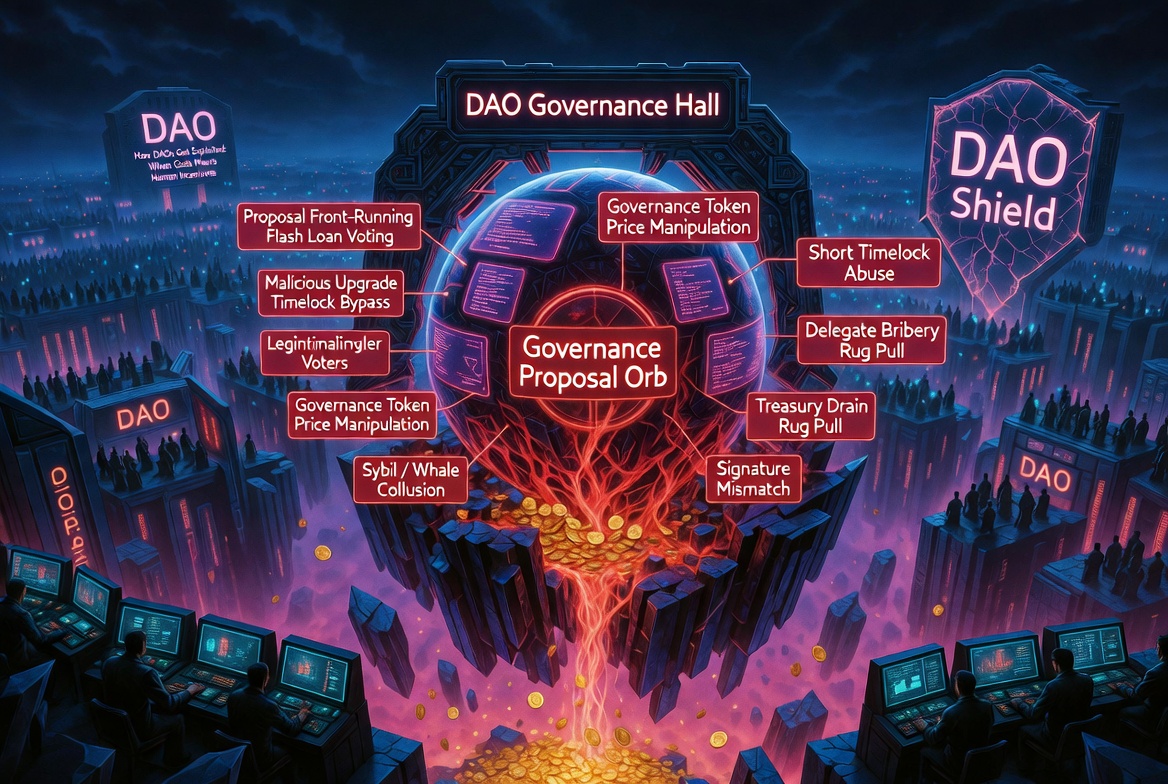
Governance Attack Vectors: How DAOs Get Exploited
Governance proposals execute with the highest privilege level in a protocol. They are also the least scrutinized code path. Here is how attackers exploit that gap.
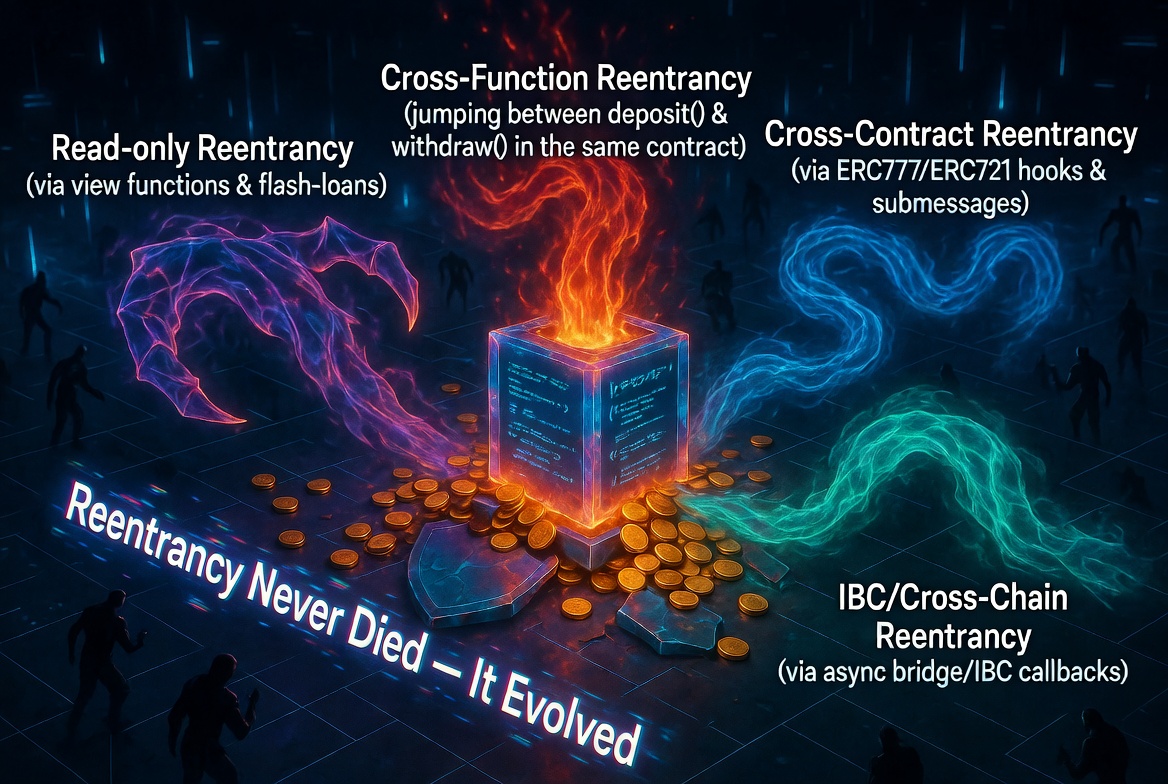
Reentrancy in 2026: The Bug That Refuses to Die
Ten years after The DAO hack, reentrancy is still draining protocols. The classic variant is well-understood. The modern variants are not. Here is what reentrancy looks like in 2026.

The Top 10 Smart Contract Vulnerabilities in 2025: Lessons from Real Exploits
2025 saw over $2 billion stolen from smart contracts. These are the 10 vulnerability patterns responsible for the largest losses, ranked by total damage.

EVM Smart Contract Security: The Developer's Practical Guide
Billions lost. Mostly to the same handful of bugs. Here is the complete practical guide to EVM smart contract security: what the vulnerabilities are, why they happen, and how to prevent them.

Solana Smart Contract Security: The Complete Guide for Anchor Developers
Anchor's macro system handles a lot. Not everything. Here are the vulnerabilities Solana programs still ship with regularly, and how to prevent them.

CosmWasm Security: The 8 Most Common Vulnerabilities
CosmWasm contracts are written in Rust, which eliminates entire classes of bugs. But the ones that remain are subtle, Cosmos-specific, and routinely missed. Here are the eight patterns that show up most often in real audits.
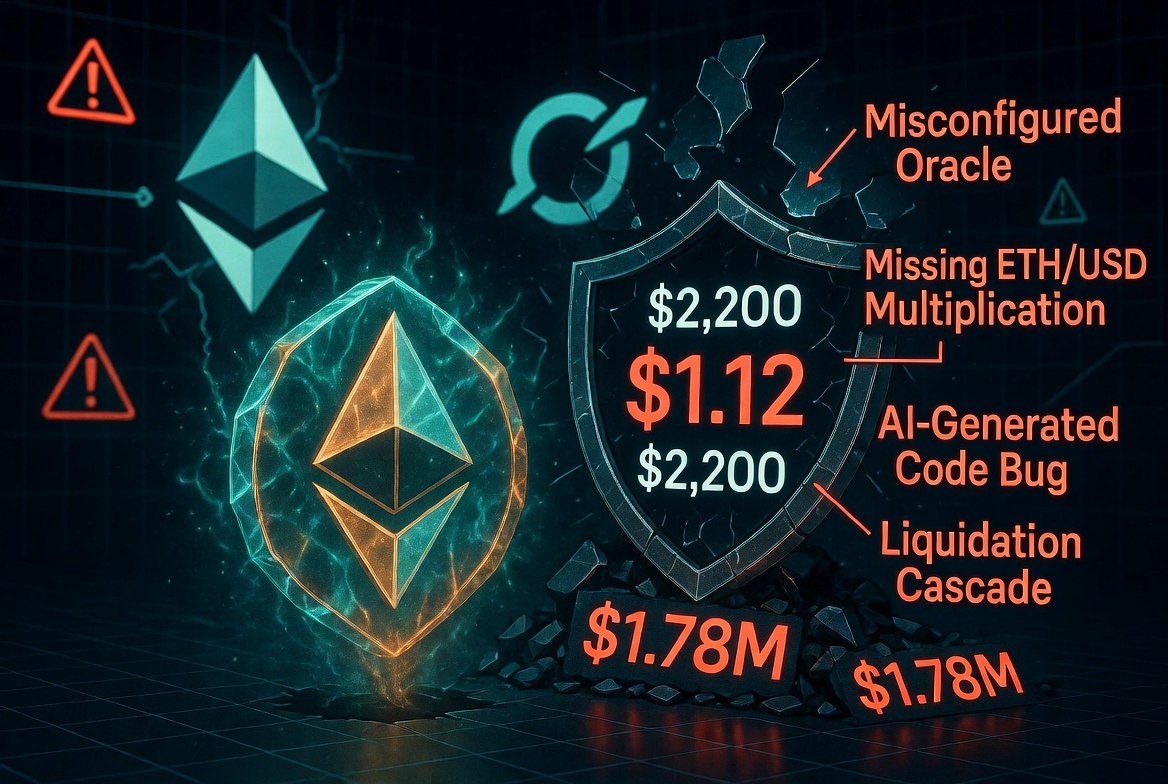
LST/LRT Oracle Pricing: The Pattern Behind $100M+ in DeFi Losses
The same misconfiguration pattern has drained protocols multiple times. LST and LRT price composition is not complicated, but getting it wrong is catastrophic.